Avoid Google File Synchronization Threats with SpinOne

Twenty years ago, if you were to mention “cloud computing” no one would have known what you were referring to. However, today in modern IT infrastructure, most enterprises are focused on placing more resources in public cloud datacenters than ever before. Aside from enterprise environments, individuals most likely are making personal use of cloud storage. What kinds of resources and services are served out from the cloud? Anything from email, applications, and all the way down to general file storage. Moving resources to the public cloud has allowed individuals and enterprises alike to be more agile, versatile, and access data anywhere.
It has also allowed enterprises to reduce tremendous expenditure in terms of capital outlay and move into a more operational expenses model. Cloud computing and specifically the accessible public cloud resources offered by today’s major players including Amazon, Microsoft, and Google has certainly revolutionized IT infrastructure.
However, with all the exciting benefits to agility, scalability, and resiliency, there are also many of the same security issues with public cloud storage as there are with on-premise file storage, especially with ransomware. Google’s cloud synchronization products such as Google Drive Backup & Sync, and Google File Stream synchronize on-premise files up to Google public cloud storage. If on-premise files are encrypted by ransomware, these are easily synchronized to cloud storage before the end user or administrators even know about it. How is that the case? Let’s take a closer look at the threat vector introduced with Google File Sync utilities and how organization files can be protected.
G Suite Backup and Sync, and Google Drive File Stream: How They Work
Let’s review G Suite Backup and Sync, and Google File Stream. Google has shown they want to facilitate the ability for both end users and enterprises to store files in the cloud – the Google public cloud. They have provided the tools to both end users and enterprise environments that allow synchronizing files from on-premise environments to cloud storage. There are two applications – Google Backup and Sync and Google File Stream that make this possible. Google Backup and Sync is the personal application that is used by home users while Google Drive File Stream is the enterprise counterpart that allows integration with Google G Suite Team Drives and allows G Suite administrator control.
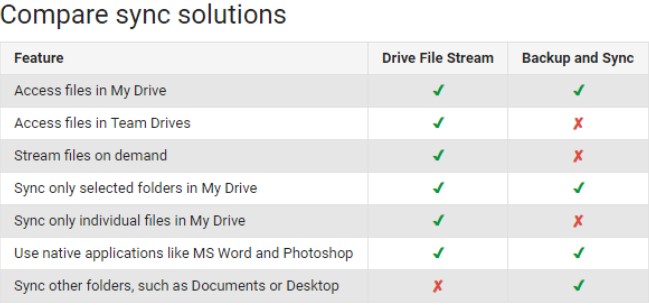
Comparison of functionality between Google Backup and Sync and Drive File Stream
Both applications are installed locally on a Windows PC and allow selecting folders for synchronization. The differences in the user interfaces of both applications include the following as noted by Google:
- Drive File Stream
- Access Google Drive like any other local or network drive
- When you access Google Drive on your computer, you see both My Drive and Google Shared Drives
- To sync content from Documents, Desktop, or other folders, you must explicitly move it to the My Drive location
- Backup and Sync
- Access google Drive like a folder on your hard drive
- When you access Google Drive on your computer, you see My Drive. You can find Team Drives only in Drive on the web.
You can select other folders on your computer to automatically backup and sync besides My Drive such as your Documents or Desktop folders.
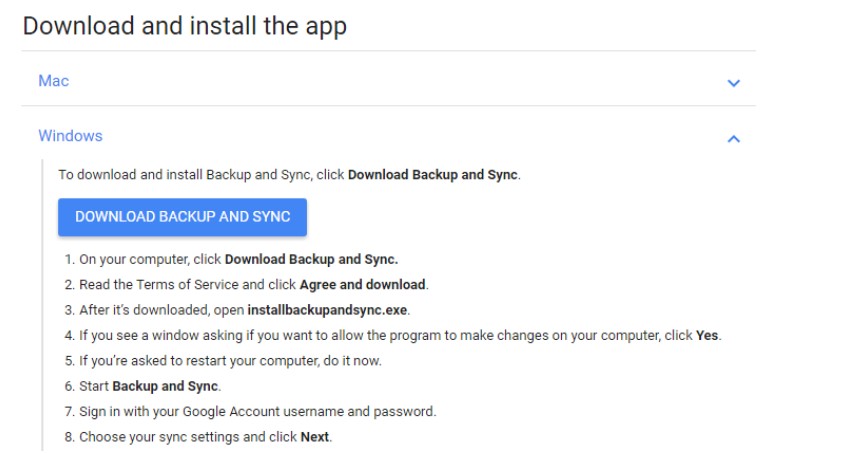
Downloading and installing the Google Backup and Sync application
After installing the application, you can start synchronizing specified folders to the Google public cloud. Notice in the preferences of the Backup and Sync application you can manually choose individual folders from your hard drive to synchronize to the Google public cloud.
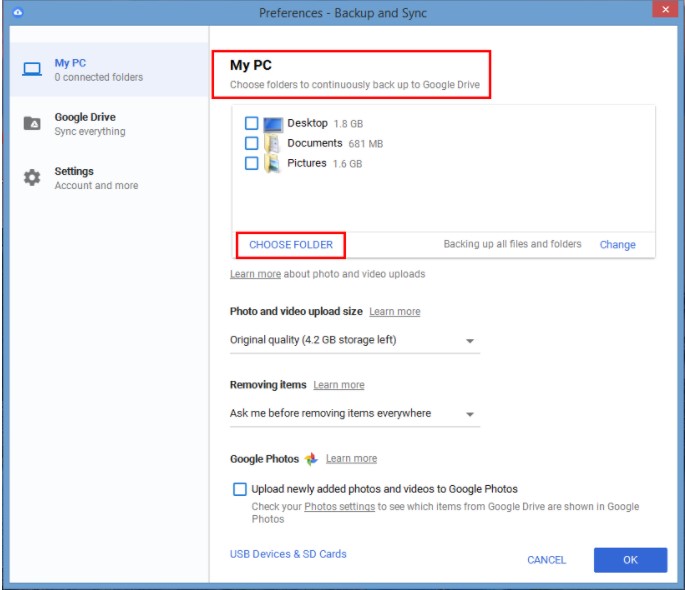
Choosing folders to synchronize with G Suite Backup and Sync
The synchronization process copies changes that are made to files locally on the hard drive to the Google public cloud. An example of a change triggering synchronization would be opening a document contained in a specified Google Backup and Sync folder, making changes to the document, and then saving the document.
While Google’s file synchronization utilities provide a great way for both home users as well as enterprise users to synchronize files from a local hard drive up to the Google public cloud, the ease of which files can be synchronized is its “Achilles heel”. Why would there be concerns with synchronizing on-premise files up to the Google public cloud?
The Ransomware Threat to G Suite File Synchronization
Arguably the most alarming epidemic to malware infections today is ransomware. Ransomware has gained much notoriety with such high-profile infections as “Wanna-Cry” and “Petya”. Ransomware is a type of malware that quietly creeps into an unsuspecting network via an email attachment, infected download, website script, or malicious ad and encrypts files found on the local hard drive or even network shares to which the end user is connected. Ransomware employs a popular form of public/private key encryption. You must “buy” the “key” from the attacker to be able to unlock any infected files.
The Ransomware infected computer communicates with a command and control server that generates the public/private key pair. The public keys are sent to the infected computer which encrypts the files based on the private key algorithm. The private key that is held by the ransomware command and control server is needed to unlock the files.
Generally, the encryption goes unnoticed until the end user or administrator notices the typical characteristics of a ransomware infection – corrupted files, odd file extensions, etc. Often, the “ransom” note is found in the directory with corrupted files directing the user to navigate to a secure, secret server to obtain the key by paying the ransom.
Ransomware presents a very real and present danger to both home and enterprise users who make use of file synchronization. Simply storing critical files in the Google public cloud does not prevent them from being encrypted, nor is it able to “magically” decrypt the files once they are synchronized to the Google public cloud. This is a common misconception that causes individuals and enterprises alike to feel a false sense of security with public cloud storage. Why are ransomware encrypted files synchronized to the Google public cloud via sync utilities such as Google Backup and Sync or Drive File Stream?
By design, a synchronization is triggered when Backup and Sync or Drive File Stream applications recognize changes to the files in the specified directories. When files are encrypted by a ransomware variant, the newly encrypted files are simply viewed as “changed” files that need to be synchronized. These files are synchronized to the Google public cloud once the user has Internet connectivity. This results in both copies of the file being encrypted and unusable – the local copy and the copy contained in Google public cloud storage.
Typically, by the time a G Suite administrator or an end user notices the encryption has taken place, the files have already been synchronized up to the Google public cloud. At this point, unless there are means to recover the files via backups, the only choices are paying the ransom, or suffering the resulting data loss.
Protect Google File Synchronization with SpinOne
The problem with the scenarios mentioned thus far is there is no easy way to recover the encrypted data once it is synchronized with the Google public cloud, whether via a home user’s Google Backup and Sync utility or an organization’s G Suite Drive File Stream. Additionally, there is no proactive protection or alerting process in place that can signal the ransomware infection is encrypting files that are actively synchronized with the Google public cloud. Organizations utilizing G Suite and home users alike, need a way to be able to effectively recover Google public cloud files as well as proactively protect their data from ransomware infection. SpinOne offers a one of a kind solution that combines powerful data loss prevention with data loss protection for Google public cloud services. This includes Ransomware Protection.
SpiOne is a powerful cloud security and backup solution that provides automatic daily backups of G Suite and personal Google account environments. This automated approach takes the “heavy lifting” out of protecting critical data from being lost. SpinOne provides protection for Google Mail, Google Drive, Google Shared Drives, Calendar, Contacts, and Sites.
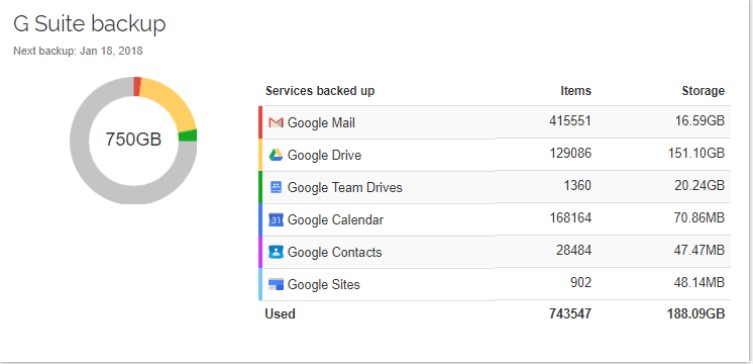
The SpinOne dashboard provides a single pane of glass view of Google SaaS services and backups
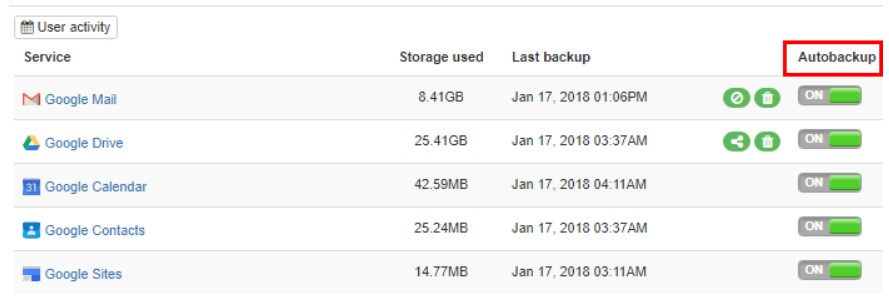
Google Services and files are automatically backed up using configurable intervals.
By utilizing intelligent and powerful machine-learning algorithms, SpinOne is able to detect and immediately remediate files that have been affected by a ransomware attack. By leveraging the automated response actions that SpinOne provides, Cloud Ransomware Protection is a powerful adversary to file synchronization threats. Ransomware Protection provides a three-fold approach to protect against ransomware infections.
- Restore encrypted files automatically – This allows SpinOne to automatically restore ransomware infected files with a good version of the file (pre-ransomware infection).
- Revoke an access – SpinOne can automatically revoke access to the synchronization app responsible for synchronizing the ransomware infected file to the Google public cloud. This stops the file synchronization process in its tracks and prevents further damage inflicted by an on-premise to cloud synchronization.
- Send notification – As mentioned, this is one of the challenges with fight ransomware – visibility to the infection. SpinOne provides proactive alerting that sends alerts when a ransomware infection is detected.
The new Custom Security Policies feature allows SpinOne Ransomware Protection and other features to be configured granularly. This allows customizing the features and functionality to the needs of your organization, business units, specific users, etc.
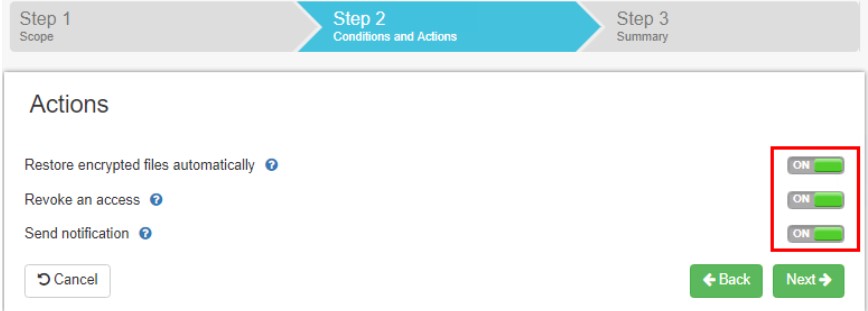
SpinOne Custom G Suite Security Policies allows tailoring Ransomware Protection settings to the needs of your organization
In addition to automatic restores, you can also manually restore any and all SpinOne-protected files. SpinOne utilizes what they call “Restore In Time Machine”. This allows restoring files from any of the restore points and offers options on where and how the file(s) will be restored.
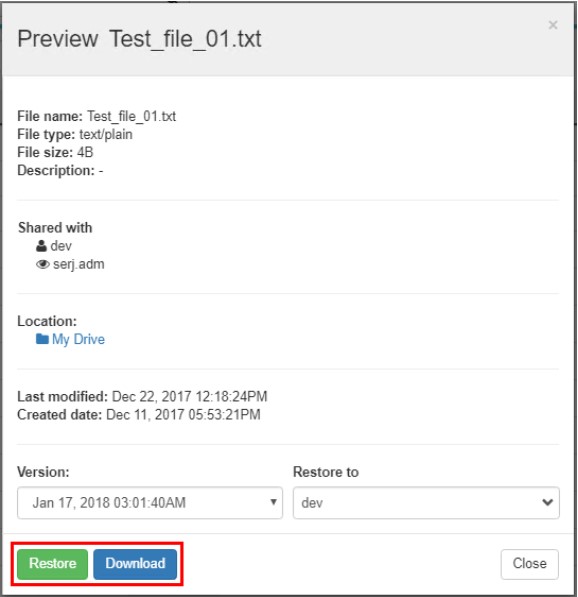
Restoring a file using the Spinbackup Restore In Time Machine functionality
SpinOne Dashboard Provides Powerful Visibility
Along with the data backup and protection features that SpinOne provides, the visibility gained by G Suite administrators empowers them with the ability to proactively manage the G Suite environment and actually see end user activities in real time. This allows detecting new threats much easier. The dashboard combined with the alerting features takes the power away from attackers and placed it with the G Suite administrator.
The Domain Audit dashboard feature allows G Suite administrators a high-level view of their G Suite domain. This includes the ability to filter events based on risk level as well as event detected.
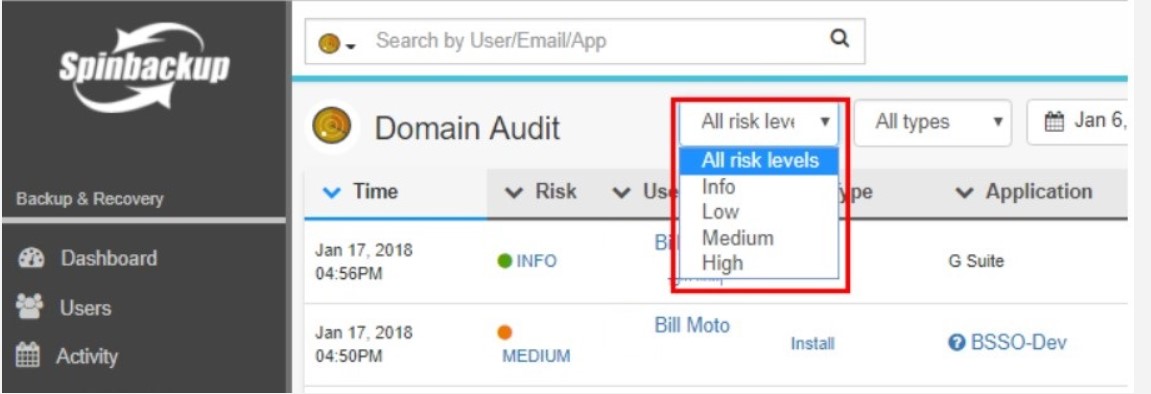
Filtering the SpinOne Domain Audit view by risk level
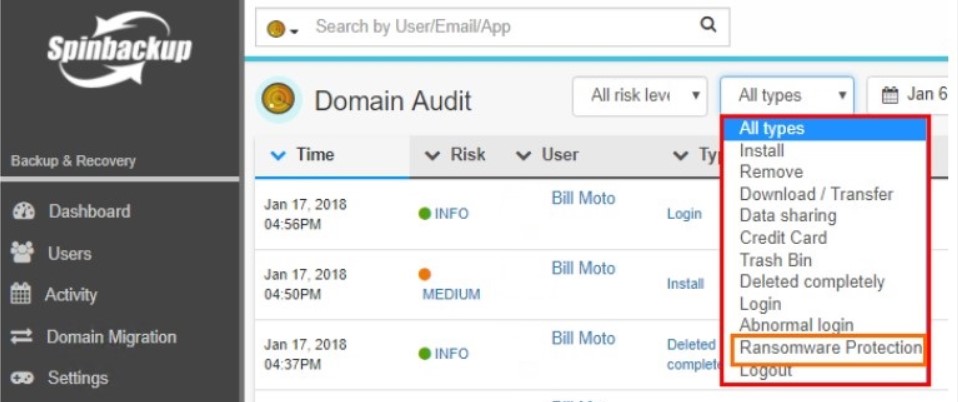
Using the SpinOne Domain Audit dashboard to view events type
G Suite administrators can see not only events related to Ransomware Protection but also additional event types related to suspicious downloads/transfers, data sharing, credit card information detection, files sent to trash bin, abnormal logins, and others.
Additionally, the Apps Audit and Data Audit dashboards allow G Suite administrators the ability to see third-party apps that have been installed and what access they currently have to G Suite resources as well as organization data that is shared with third-party users.
When you combine the ability to backup Google SaaS data with the visibility that is gained into organization activities, SpinOne provides the total solution to protect your Google data from ransomware and many other threats to data being leaked or lost.
Concluding Thoughts
Ransomware is a serious threat to both personal and enterprise data. With more data being synced to various public cloud providers, having ransomware infect on-premise files and synchronize up to the public cloud is security concern that must be addressed by everyone taking advantage of file synchronization utilities.
Google file synchronization utilities such as Backup and Sync and Drive File Stream are not immune to synchronizing ransomware infected files to Google public cloud file storage. Good versions of files stored in the Google public cloud are overwritten with the ransomware infected versions.
Without good backups, data could be lost forever. SpinOne is a solution that provides a powerful all-in-one approach including both backups and security measures to prevent ransomware destroying data. The automated daily backups protect critical data while features like Ransomware Protection proactively remediate ransomware infections. It does this by automatically restoring good versions of files, revoking access to the offending synchronization utility, and alerting administrators.
SpinOne meets and exceeds the threats presented by today’s malware including ransomware. By protecting your Google data with SpinOne, you can have confidence in public cloud storage and utilize the benefits afforded by file synchronization utilities.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Importance of Backing Up Google Workspace Data Daily
January 23, 2024Many organizations today are heavily relying on cloud Software-as-a-Service offerings for business productivity, communication, and... Read more
Google Workspace in 2024: Key Updates and Features
December 14, 2023Google Workspace is constantly improving to bring new productivity features for businesses. In this article,... Read more
How to Implement Data Leak Prevention in Google Workspace
October 27, 2023Data leaks in Google Workspace can have severe legal, financial, and reputational implications for the... Read more


