Cybersecurity Vulnerability: Definition, Types & Detection Ways

What is cybersecurity vulnerability?
Cybersecurity vulnerability can be defined as a weakness in an information system that provides an exploit opportunity for existing cyber threats. Both criminals and security professionals are looking for such weaknesses to use or to remove them.
Vulnerability Types
Vulnerabilities fall into several categories:
By location:
- On-premise network or Cloud
- Software (OS, apps) or Hardware
- Defense system or Basic infrastructure
By nature:
- Procedural vulnerabilities.
Some processes are missing or organized incorrectly. As a result, they expose the entire system. Procedural vulnerabilities are harder to detect because you need to assess all the business processes.
Examples:
- Public access to sensitive information or PII;
- Lack of cybersecurity training for employees;
- No data backup.
- Architectural vulnerabilities.
When building an information system, IT experts can miss some essential components or use parts that have an inherent weakness.
Examples:
- Software without compliance certification;
- Applications that aren’t updated on a regular basis;
- Lack of antivirus software.
- Human error vulnerabilities
Human errors are inevitable. That’s why not only do they account for multiple cyber incidents but also the majority of modern cyberattacks rely on this type of vulnerability.
Examples:
- Accidentally deleting an important file;
- Entering a password in a crowded environment;
- Not checking the address of an email sender.
Shadow IT
It’s a special type of cyber vulnerability. Shadow IT is any software or hardware that employees use without the approval of an IT department. Those in charge of cybersecurity don’t know about shadow IT and therefore can’t monitor and control it.
Finding Cybersecurity Vulnerabilities
- Monitor cybersecurity incidents that occur with other businesses. This will give you an idea of the existing threats and what vulnerabilities they employ.
- Create a cybersecurity policy for your company. Make sure everyone complies with it. The policy should contain penalties for non-compliance.
- Audit your network, its components, and how they interact with each other. You should also check how people employ the information system.
- Conduct penetration testing once in a while. It will help you detect the gaps in your defense.
- Acquire vulnerability protection software. Install antivirus software and tools that detect shadow IT.
- Train your employees on a regular basis. People tend to forget about threats and relax. That’s when they turn vulnerabilities into damages.
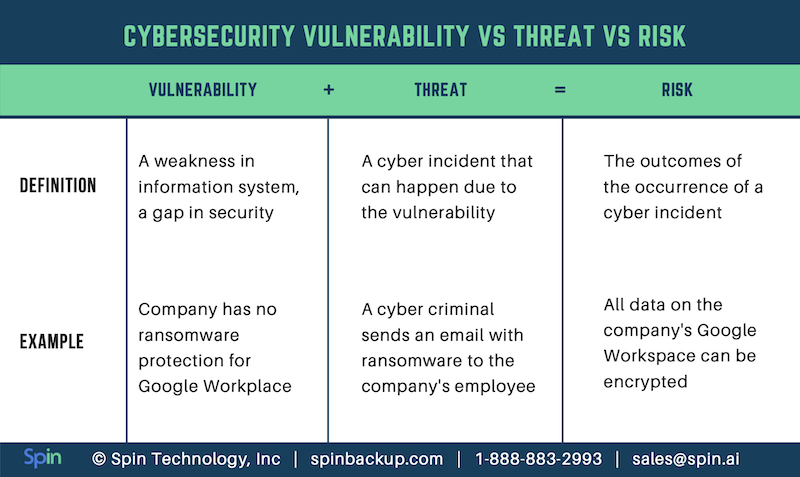
Vulnerability vs. Threat vs. Risk
People often confuse vulnerabilities with risks or threats. However, there’s a major difference between these terms.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Protecting Partner Margins: An Inside Look at the New Spin.AI Partn...
April 2, 2024Google recently announced a 40% reduction in the partner margin for Google Workspace renewals –... Read more
Top 10 Salesforce Security Best Practices and Tips
February 28, 2024In the ever-evolving threat landscape, safeguarding sensitive data is paramount. Salesforce, a leading customer relationship... Read more
Microsoft 365 Security Best Practices and Recommendations 2024
February 9, 2024Micorosft 365 is a business-critical cloud environment that contains terabytes of sensitive information. Protecting this... Read more