How to Avoid Becoming a Cybercrime Victim

In the previous post we have covered the cyber security topics of suspicious files and links, password creation and 2-step verification. Let’s discuss OS and software, antivirus, backup, mobile security, physical security and so on.
Operating System and Software
- Do not use pirate software. Do not run and install software downloaded from unsafe sources, including torrents and other peer-to-peer file sharing. It is not about morality or ethics – it is simply unsafe. First, software distribution infection with the Trojan and its “free” publication on the Internet is a well-known way of system infection, and it happens far more often than we would like. Second, security updates can rarely be installed on pirate software. “Activation” and reactivation will spend your time, and the risks of software not updating are inadmissible.
- Enable Auto-Update in your Windows OS.
- Make sure Windows auto-update is set up for checking all Microsoft products updates, including MS Office.
- Update 3rd-party applications regularly and automatically.
- Enable Auto-Update in AppStore.
- Enable MS Office Auto-Update in Mac OS.
- Use Homebrew for updating your 3rd-party apps.
- Modern Linux distribution provides a possibility to set up auto-update via OS services or regularly update software manually.
Antivirus
- For Linux or Maс OS do not use antivirus. Seriously. Security solutions are vulnerable; they are not safer than any other software. Besides, for effectiveness, antiviruses usually require higher privileges in OS. It possesses higher risk than virus or trojan infection threat at relatively safer and less popular platform. If you follow other recommendations from this guide, you can install antivirus that will not constantly monitor your OS and periodically scan your system with it.
- For Windows use antivirus. But do not forget antiviruses are very ineffective against modern online-threats.
- It is difficult to select an antivirus: “independent” tests are more favorable to antivirus-vendors that ultimately finance these tests. However, there are several more or less objective reviews and tests results.
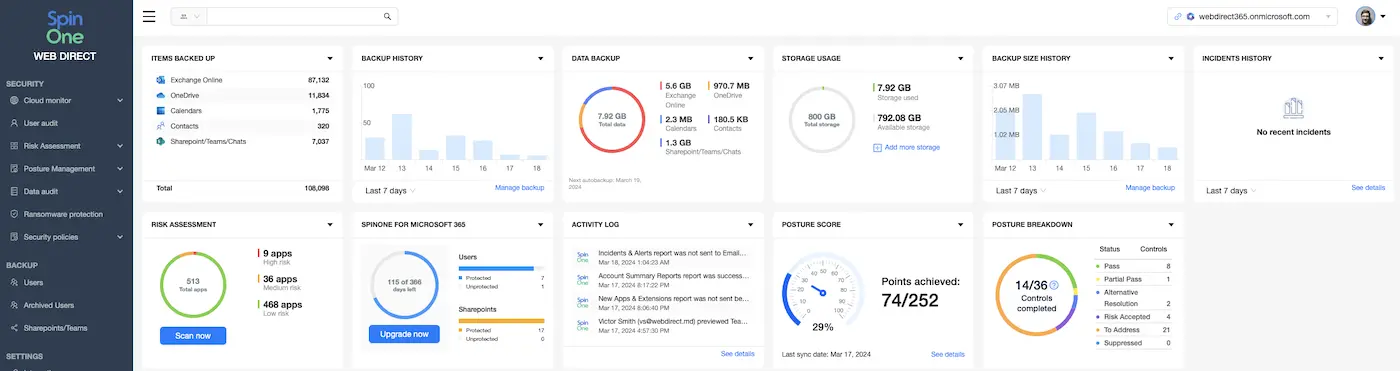
G Suite Backup
- At least, use a separate ciphered external hard disk. Connect it EVERY TIME you work on something important. The recommended disk storage is at least twice as big as your internal one.
- Alternatively, choose an outside backup-provider for automated daily backup.
- You can do backup saving the files in the cloud, as Dropbox, iCloud Drive, OneDrive, G Suite. But do not forget to encrypt your data before uploading and backing up the cloud. The most secure way is to use a 3rd-party cloud-to-cloud backup provider that uses encryption for backup to protect your cloud data.
Use Cryptography
1. Check your website ciphering
Always make sure the web-site you upload your sensitive data uses HTTPS secure protocol. Its address starts with “https://” and its certificate is checked by your browser, so it doesn’t make security alerts to you. Please pay attention that HTTPS is not enough for creating trust to the site: anybody can generate an active certificate for his web-server. Pay attention and check the web-site domain name correctness because it can be easily fabricated. Never, even for temporary use, accept invalid certificates.
2. Cipher data
You may use your operational system Full Disk Encryption function for protecting data at your notebook or PC from loss or theft.
You can also cipher external disks or separate files.
3. Encrypt sources of connections
Use reliable end-to-end encryption for corporate and private confidential data transit. End-to-end encryption guarantees nobody but you and your recipient will receive access to conversation. End-to-end encryption means email are PGP / GPG and S/MIME. You can also use mobile encryption apps.
Mobile Security
- Mobile network is as dangerous as public Wi-Fi spots. Use the same cryptographic services for your mobile network data transmission. Do not consider your SMS or voice conversations private: use voice calls and messages that are end-to-end encrypted instead.
- If Android, then Google. Only direct OS support by the developer can guarantee timely security updates. Any additional links decrease the security level. Sometimes, updates stop working for your device after a year or two.
- Do not root your smartphone. Use only allowed application sources, as Google Play and AppStore. Do not download or install “security updates” from unauthorized software sources.
Physical Security
- Keep your staff where you can see or control it. Your computer and devices require the same physical security level as your credit cards and automobile keys. Remember: if a bad guy spends even a short time alone with your computer, the computer will become not yours, but his. Most likely, he can compromise your system without huge efforts. Blocking user’s session can help, but there are modern attacks that cannot be secured by this. So, don’t leave your device unattended, especially when turned on. Turn it off or make it sleep every time you leave it unattended even for several minutes. Enable password request every time it turns on.
- Provide sensitive and non-sensitive operations from different computers. If you allow children to play online games on the computer that you use for online business, you are going to be hacked. If you send business emails from open hotel wifi, you are going to be hacked. Use separate computer for business and financial operations and all types of actions that require privacy or confidentiality. Use special virtual or physical device for the most critical operations.
Protect Yourself!
Thanks for paying special attention to your own cyber security. Share this article with your friends and colleagues to make the world a little bit more secure.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Importance of Backing Up Google Workspace Data Daily
January 23, 2024Many organizations today are heavily relying on cloud Software-as-a-Service offerings for business productivity, communication, and... Read more
Google Workspace in 2024: Key Updates and Features
December 14, 2023Google Workspace is constantly improving to bring new productivity features for businesses. In this article,... Read more
How to Implement Data Leak Prevention in Google Workspace
October 27, 2023Data leaks in Google Workspace can have severe legal, financial, and reputational implications for the... Read more


