32-Step PCI Compliance Checklist for Reference & Self-Check

Does your company accept credit card payments from customers but lack practices for securing this information? If yes, you are walking on thin ice by risking your customers’ financial safety and your credibility as a company. But you, apparently, know that all already—that’s why you are here.
What you should understand in the first place is that you can’t just tick all the checkboxes and meet PCI standards once and for all. Making your business PCI DSS compliant is not a result but an ever-going process of bettering your security.
But before we dive into the requirements and the checklist itself, let’s quickly walk through the basics first.
What is PCI DSS compliance?
PCI DSS stands for Payment Card Industry Data Security Standards and is a commonly recognized regulation created by card issuers for securing cardholder information. It sets out guidelines and outlines 12 requirements for companies that process, store, or transfer customer payment information.
Is PCI compliance mandatory? Yes. Every company that interacts with cardholders’ payment information must adhere to the PCI DSS regulations. Otherwise, the company will suffer high penalties, lawsuits, and client losses.
Four PCI Levels
PCI compliance consists of four levels determined by the number of transactions a company conducts per year:
Level 1: Business that processes more than six million Mastercard, Visa, or Discover transactions, more than 2.5 million American Express transactions, or over one million JCB transactions.
Validation requirements for level 1:
- Annually submit the compliance report conducted by a qualified security assessor
- Perform a Quarterly Scan your Network (QNS) for vulnerabilities with the help of an approved scan vendor
- Attestation of compliance report
Level 2: Business that processes between one to six million Mastercard, Discover, or Visa transactions, within 50,000 to 2.5 million American Express transactions, or up to one million JSB transactions.
Validation requirements for level 2:
- Annually conduct a Self Assessment Questionnaire (SAQ)
- QNS
- Attestation of compliance report
Level 3: Business that run from 20,000 to one million Visa, Mastercard, or Visa transactions, and up to 50,000 American Express transactions.
Validation requirements for level 3:
- The same as for Level 2
Level 4: Business that handles 20,000 or fewer transactions per year.
Validation requirements for level 4:
- These depend on the merchant’s bank and include SAQ and QNS.
The higher the level, the more intense and resource-consuming the validation requirements.
12 PCI Security Standards
You can see that these levels determine how assessors will evaluate and validate your company. But no matter what level you are at, you have to go through the same 12-step routine to ensure your systems and network are secure.
To meet the PCI compliance standards, or at least to be on the way to it, you need to walk through the six main security goals and twelve requirements that help to meet these goals.
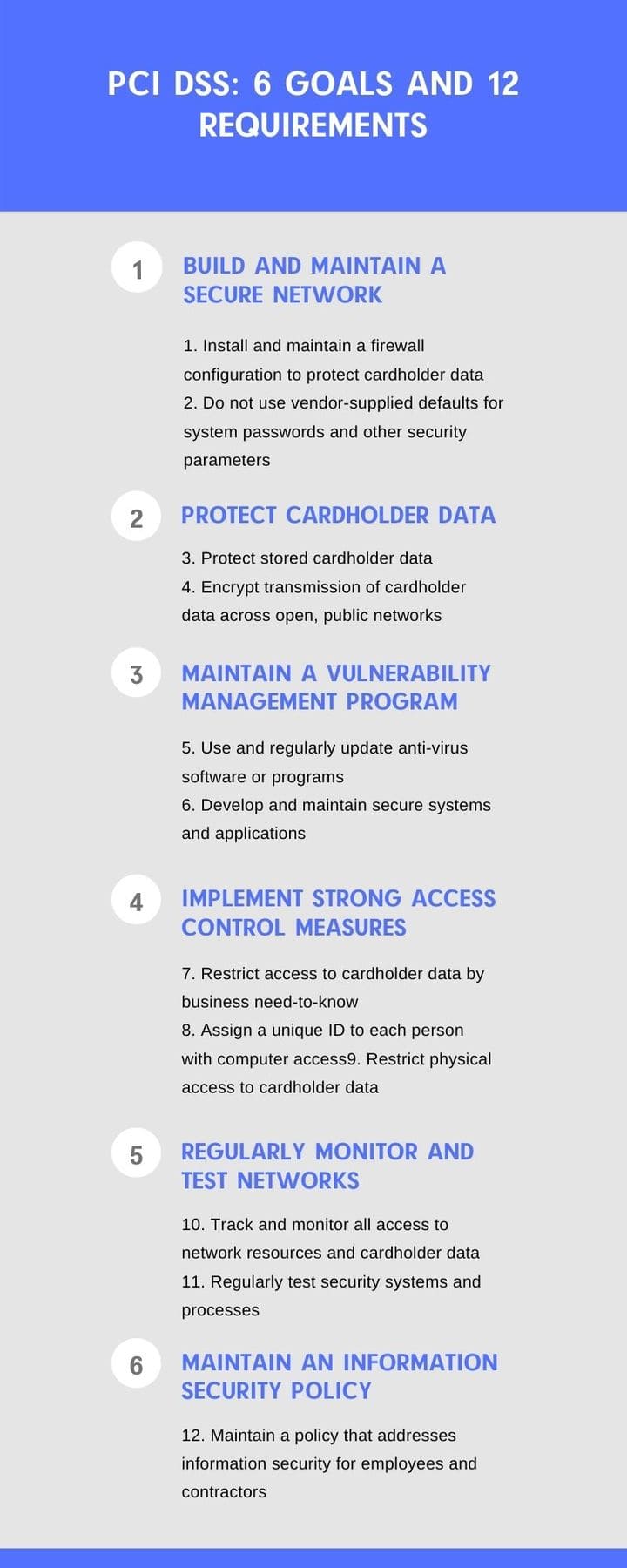
All card issuers officially set these goals and requirements, which encompass technical and operational systems involved in operations related to all cardholder data.
PCI DSS Compliance Checklist
This simple infographic should’ve provided you with a general understanding of PCI security elements. Now, let’s be more specific about what exact steps you should take to comply with them.
All the checklist points we’ve outlined here agree with the 12 mentioned requirements. We designed this checklist to assist you in self-auditing and working your way through the steps you need to complete.
Don’t approach this checklist as an official document or its replacement. It also won’t substitute the professional assistance of the compliance authorities and security specialists. Instead, consider it a self-check that guides you to data security and IT compliance.
- Set up and deploy a firewall and configure router standards; be sure to revise these sets of rules and configurations every six months;
- Ensure these configurations restrict all the inbound and outbound traffic that 1) comes from unreliable sources (like a public network) and 2) is unnecessary for the cardholder data environment.
- Ensure all devices, whether company-owned or employee-owned, that can access the cardholder data storage have personal firewall software for security.
- Make sure to have a documented policy that includes all the practices regarding firewall security and make it accessible to all the parties involved.
- Disable all the default settings, passwords, parameters, and accounts, and make sure to do so before connecting the system to the network environment.
- Compose a set of rules and standards regarding password creation and storage.
- Configure strong passwords for all the systems using your password guidelines.
- Secure credit card information both in transit and at rest using robust encryption practices.
- Secure encryption keys from exposure or misuse.
- Implement SSL/TLS security protocols to protect data during transmission over unreliable public networks.
- Make sure no one will share unencrypted PAN codes via messaging.
- Create a security protocol, list all the internal systems, possible threat vectors/vulnerabilities, and address them with industry-recognized solutions.
- Ensure your hosting providers have a security policy that protects all the data you store on their services.
- Set up robust endpoint protection (antivirus) across all the company devices, or at least on those to access cardholders’ data. Be sure to schedule regular reviews of the software to update and patch the software in time to avoid security vulnerabilities.
- Schedule regular system vulnerability testings; you can do so by using special scanning services.
- Establish a process for the in-time addressing and maintaining of all the found vulnerabilities.
- Ensure that you protect access to the cardholder data within your organization to prevent any unauthorized employee from obtaining it.
- Determine who needs to have access to the data within your organization and what for. Weigh all the risks before providing users with cardholder information.
- Make sure every user in your company has a unique user ID and user name.
- Enable access-management standards that are controlled by your administrator.
- Turn on multi-factor authentication for all users and third parties so they can securely access systems remotely.
- Determine the retention policy applicable to your situation and store data for as long as it tells you to. Don’t store data longer than you should and don’t hold onto data you don’t need for business or legal purposes.
- Delete sensitive authentication information after authorization.
- When showing PAN data, always mask it; all you can show is the first six and last four digits.
- Secure all the physical devices (computers, notebooks, servers) that contain cardholder information.
- Conduct domain, data, and third-party application audit daily using specially designed services.
- Protect electronic and paper mediums with sensitive information on them.
- Monitor critical files to ensure they aren’t accessed or modified without permission.
- Create an internal cybersecurity policy that addresses PCI DSS goals and requirements, explaining to users what they can and can’t do within the work system. Review this policy every six months.
- Conduct a background check of all the employees you hire to reduce the possibility of insider attacks.
- Have a versioned backup of your data stored on different carriers.
- Create a step-by-step incident response plan that is easily and quickly executable in case of a data breach.
Remember: this checklist is designed as a self-audit tool, not as a standard for your PCI compliance assessment. The official PCI standard consists of around 300 obligatory measures for merchants and other organizations. And yet, by self-checking with this checklist, you will be able to find the existing gaps and weak spots in your security, which will come in handy for the PCI audit.
Also, do not neglect cybersecurity tools that facilitate and simplify the process of becoming compliant. Using some of these tools may speed up the process, making it less complex and more debugged.
As a multilayered process, meeting PCI compliance requires many different tools and practices for you to incorporate. But you can simplify this process, using a two-in-one cybersecurity tool Spin, that protects G Suite and Microsoft 365 users from both data loss and data leaks.
Using Spin, you kill two birds with one stone:
- You reduce insider threats – sensitive (cardholder data) and business-critical data sharings and downloads, intentional data deletions.
- You reduce outside threats – unauthorized access, credential stuffing, and password spraying, ransomware, threats posed by risky applications.
These include the following:
- SpinBackup – automated, secured, backups of your G Suite and Office 365 environment
- SpinSecurity – Automated AI-powered ransomware protection and cybersecurity features for the cloud
- SpinRDR – Automated audits of third-party apps and browser plugins, 24/7 monitoring, security policies, and the ability to blacklist apps or extensions
Want to know more about how exactly it works?
Frequently Asked Questions
Is PCI compliance mandatory?
There is no a specific law to mandate PCI DSS compliance in the US, yet it is required by the payment card industry to safeguard cardholder data and maintain the security of financial transactions. Payment card companies, such as Visa, MasterCard, American Express can impose penalties on businesses that experience a data breach or do not safeguard safeguard cardholder’s data sufficiently. These penalties may include fines and restrictions on processing credit card payments. Thus, if your organization handles credit card transactions or stores, processes, or transmits credit card data, PCI DSS compliance is essentially required.
What are the four (4) PCI compliance levels?
PCI DSS categorizes organizations into four (4) different compliance levels based on their annual volume of credit card transactions. These include:
- PCI Merchant Level 1 (over 6 million transactions annually, across all channels, or any merchant that has experienced a data breach)
- PCI Merchant Level 2 (between 1 to 6 million transactions annually, across all channels)
- PCI Merchant Level (between 20,000 and 1 million online transactions annually)
- PCI Merchant Level 4 (less than 20,000 online transactions a year or any merchant processing up to 1 million transactions per year)
What are the 12 PCI standards?
PCI DSS outlines 12 high-level standards designed to secure credit card data and protect it from theft and fraud. Each of these standards has multiple requirements and sub-requirements. Here are the 12 PCI DSS standards:
- Install and maintain a firewall configuration to protect cardholder data;
- Do not use vendor-supplied defaults for system passwords and other security parameters
- Protect stored cardholder data
- Encrypt transmission of cardholder data across open, public networks
- Use and regularly update anti-virus software or programs
- Develop and maintain secure systems and applications
- Restrict access to cardholder data by business need to know
- Assign a unique ID to each person with computer access
- Restrict physical access to cardholder data
- Track and monitor all access to network resources and cardholder data
- Regularly test security systems and processes
- Maintain a policy that addresses information security for all personnel
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Reducing Browser Extension Risk with Spin.AI Risk Assessment + Perc...
April 24, 2024Spin.AI is collaborating with Perception Point: integrating the Spin.AI Browser Extension Risk Assessment within the... Read more
How to Restore A Backup From Google Drive: A Step-by-Step Guide
April 10, 2024Backing up your Google Drive is like making a safety net for the digital part... Read more
Protecting Partner Margins: An Inside Look at the New Spin.AI Partn...
April 2, 2024Google recently announced a 40% reduction in the partner margin for Google Workspace renewals –... Read more


