SOX Compliance Checklist and Requirements

Following multiple financial scandals in the 1990s, it became clear that the United States gravely needed legislation to prevent fraud or misinterpretations in financial reporting. That’s how Sarbanes-Oxley Act came to be. Abbreviated SOX, the act was adopted back in 2002.
Although more than 20 years have passed since its adoption, many companies still struggle to follow its regulations. We prepared SOX Compliance Checklist to help businesses with meeting the SOX requirements.
In this article, we’ll figure out:
- What is SOX compliance?
- SOX compliance checklist
- Tips on meeting SOX compliance goals
Even if you are not required to meet the SOX compliance requirements right now, our SOX audit checklist will help you with self-assessment and preparation for the future.
What is SOX Compliance? Short Overview
Sarbanes-Oxley Act was created in response to businesses meddling in their financial reports and deceiving investors. It lays down the regulations to make business activities transparent.
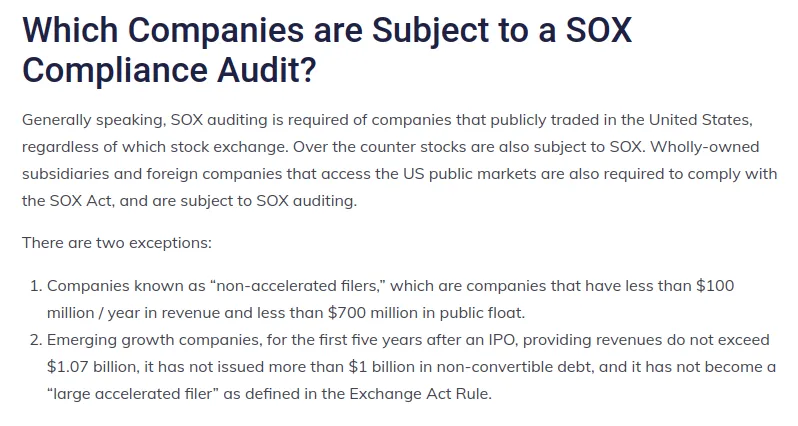
First and foremost, SOX regulates U.S. public companies. In some cases, private companies and non-profit organizations need to comply, as well. Also, this compliance impacts non-U.S. companies operating in the U.S. To stay compliant, all companies must pass a SOX compliance audit―a procedure of assessing a company and its internal controls.
Regulations protecting the records of a business comprise a large portion of overall SOX rules. Taking into account modern business practices, it often means the protection of your digital data stored in corporate clouds like G Suite and Office 365.
One of the core goals of SOX regulatory compliance is to make financial reporting transparent. The non-compliance may result in monetary penalties up to $5 million or even imprisonment. An organization’s CEO and CFO (or equivalents) have responsibility for financial reports and their accuracy.
The act consists of sections covering corporate responsibility for financial reports, management assessment of internal controls, and other issues. They are highlighted in the full text of the Sarbanes-Oxley Act.
Let’s take a look at the Sarbanes-Oxley compliance checklist and what actions you can take to improve the transparency and security of your data.
SOX Compliance Checklist
The following SOX compliance IT checklist will help you to secure your system and align it better with the record protection requirements.
Create a complex system for security breach detection. It should comprise tools, policies, practices, and people responsible for implementing them.
Let’s take ransomware attacks as an example. You need to have:
- a tool that detects this type of malware, e.g., SpinOne for Google Workspace and Microsoft 365
- a plan for how to stop the attack (SpinOne will do it automatically after detection).
- Incident Response Plan that stipulates what should be done after the attack, like data recovery (SpinOne does it automatically)
- an IT security team to respond to a ransomware attack
Build a system for data loss prevention. Similar to security breach detection, this system should comprise tools, policies, practices, and people.
Large SaaS products like Google Workspace and Microsoft 365 have incorporated DLP policies. However, often, they aren’t enough to meet the data loss challenges and cases. That’s why we suggest third-party tools like SpinOne that will enable you to:
- detect abnormal logins
- detect abnormal data behavior
- backup and recover your records
- stop ransomware during the attack
Make a data protection system that operates 24/7. Cybercriminals are scattered around the world and won’t wait for your business hours to strike. Furthermore, modern cybersecurity threats outnumber the capabilities of any IT team.
That’s why the basis for corporate data protection systems should be IT security automation. For example, SpinOne automates such important functions as backup, application detection and assessment, and data leak and loss prevention.
Create a data leak prevention system. You need to protect your files from exposure to unauthorized people. Use tools that will enable you to monitor and control improper sharing settings, sending sensitive data via email, and mass copying of records.
Create an incident notification system and reporting. Use tools to alert your IT security team about potentially risky cyber events. For example, in SpinOne, you can send alerts by email or corporate messengers. Reporting is another essential part of such a system.
It enables your team to see the trends in implementing your IT Security strategy and patterns in attacks and threats.
Provide SOX auditors access to the necessary information. The auditors will require your financial data and information on how you secure this data. Prepare a document that will cover every aspect of your data protection.
How SpinOne Helps You to Meet SOX Compliance Requirements
SpinOne for Google Workspace helps you to protect and monitor your data in order to meet IT security compliance requirements. That’s what our security software can do for you.
- Automated daily backup for Google Workspace and Microsoft 365.
- AI-based ransomware detection and prevention.
- Monitoring of domain activities (including user logins and login attempts).
- Detection of Shadow IT and evaluation of the risks of SaaS apps and extensions.
- Automated data audit to detect potentially dangerous activities, like sharing credit card information via email.
Get a demo to find out more about our cybersecurity products for G Suite and Office 365.
Learn More About Data Security Compliance
SOX is not the only compliance standard you may need to follow in your daily business activities. We recommend reading more about HIPAA, NIST, or GDPR to ensure your data security meets the highest standards.
Check out the cloud data security and compliance best practices for Google Workspace and Microsoft 365.
Here, you can read how our security products help you to protect your data and stay compliant.
Frequently Asked Questions
What does SOX mean?
SOX stands for the Sarbanes-Oxley Act. This act was created to protect investors from instances when businesses presented fake financial reports to deceive them and get investment.
What are the controls of SOX?
Sox controls are any controls that are relevant to Sox compliance. They include the controls of corporate governance, access, business processes, change management, data backup, and segregation of duties.
What is SOX checklist?
SOX checklist includes 6 activities:
- Create a complex system for security breach detection.
- Build a system for data loss prevention.
- Make a data protection system that operates 24/7.
- Create a data leak prevention system.
- Create an incident notification system and reporting.
- Provide SOX auditors access to the necessary information.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Salesforce GDPR Compliance Guide for Businesses
November 8, 2023GDPR is a key data protection regulation document for all companies that want to work... Read more
SOC 2 Compliance Guide for Google Workspace
June 28, 2023Security and privacy are paramount with cloud computing and Software as a Service (SaaS), ensuring... Read more
ISO Compliance Guide for Google Workspace Administrators
June 22, 2023ISO compliance has been a buzzword in data protection circles for quite some time. In... Read more


