How Does Ransomware Work in the Cloud?

Ransomware is one of the major cybersecurity threats to organizations worldwide. The accumulative cost of downtime caused by ransomware reaches hundreds of billions of dollars yearly in the US alone. Learn how ransomware works in the cloud.
How Ransomware Works in the Cloud
Ransomware can hit the cloud just like it hits on-prem. It encrypts text files (e.g., documents and spreadsheets) and emails. When opening the infected files, the victim can see a ransom message in the beginning, requesting to send a certain amount of money to the cybercriminals that successfully infiltrated the system.
Unlike on-prem analog, cloud ransomware doesn’t proliferate as a downloadable file. Instead, it works as any SaaS application.
SaaS apps gain OAuth access to the data stored in cloud office suites like Google Workspace or Microsoft 365. An employee subscribes to the apps using their working account in these environments. They also provide reading and editing permissions.
The editing permissions give the green light for the ransomware to change any information stored in corporate GW or MS365, i.e., encrypt the files. Without a decryption key, it is almost impossible to restore these files unless you have a backup.
However, any restored file can be decrypted again until the OAuth access of ransomware to your cloud environment is revoked by the Admins.
There are several ways that ransomware can get the OAuth access:
1. Social engineering
This attack usually includes some type of phishing email. It tricks an employee into using ransomware and granting it OAuth access to the cloud office suite. For example, it can pretend to be a bank website that requires a person to log in.
2. Zero-day attack
This attack happens as a result of a vulnerability exploit of a legitimate application. Hackers are constantly searching for bugs in such applications and the ways they can use these bugs to attack users of these applications.
3. Credential theft
Finally, hackers can acquire the credentials of a user to infiltrate in the system. In this case, they will often first try to steal as much information as possible and only then unleash the attack.
Encryption Process
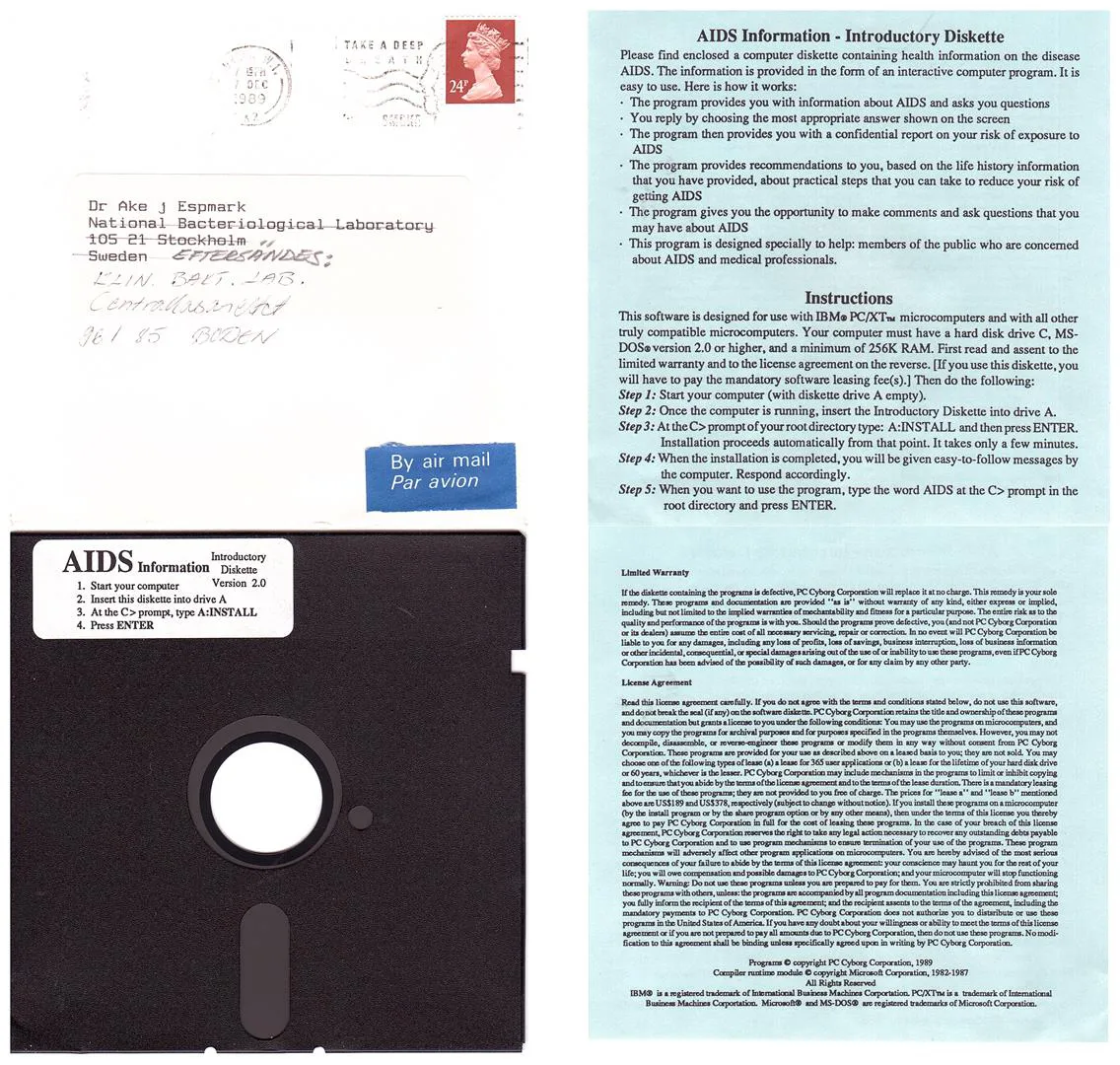
The first ransomware, AIDS Trojan, sent in 1989 by Dr. Joseph Popp encrypted only file names and contained a decryption key in itself. Thus the victim didn’t have to pay the malware creator to regain their data.
This type of encryption is called symmetrical, in which the sender and the recipient of the message use one key for encryption and decryption.
Seven years later, cryptographers, Adam L. Young and Moti Yung theorized that asymmetrical encryption is more efficient for “cryptovirus extortion.” They successfully created the virus and carried out the attack on Macintosh SE/30 simply to prove their hypothesis. Furthermore, they publicly presented their findings at the 1996 IEEE Symposium on Security and Privacy and even summarized them in a scientific paper.
Asymmetrical encryption uses two keys: private and public. The public key is used to encrypt the text. It can be distributed publicly without the risk of being “cracked.” For decryption, you need the private key.
This key is kept secret and protected by the ransomware developer. Once it is made public, the value of the ransomware is diminished and anyone can decrypt it without paying the criminals.
In 2013, almost 20 years after Young and Yung published their findings, ransomware gained momentum. And today we see its devastating impact on businesses and individuals who became victims of ransomware attacks.
The ransom demands have skyrocketed to 7-figure sums, dozens of new strains are released into the wild every year, and new ways to blackmail victims into paying money emerge. The encryption principles remain the same.
Most ransomware strains use asymmetric encryption. Some use a combination of symmetric and asymmetric methods.
Recently we’ve seen a new technique used by ransomware strains, intermitten encryption. This type of encryption doesn’t hit all the files in the infected system. Instead, it searches the files that meet certain criteria. Usually, it is a file size, or creation date, file owner, or the keywords (e.g., financial”). An example of such ransomware strain is Rorschach which managed to encrypt 220K files within 4.5 minutes and is considered the fastest ransomware today.
Extortion methods
Extortion is an important aspect of any ransomware attack. The first extortion attempt was performed by Dr. Popp who demanded $189 in exchange for decryption.
Young and Yung in their model proposed an idea of encrypting digital money and a promise to decrypt it in exchange for half of the sum. They said that since the victim cannot access encrypted digital money, they will be willing to pay half of it only to get at least part of it back.
Their prediction about digital money hasn’t come true. However, criminals don’t need to do it. It’s enough to just hold hostage the data that enables the business to earn its money.
For example, in the November attack on an indie game by Gellyberry Studios, criminals managed to encrypt all information about the 17K player accounts that includes the ingame items and game progress. It’s enough to make many players leave the game and never return again, a severe strike on a startup company that exclusively depends on subscriptions.
In the past many companies were forced to pay ransom out of the fear of losing their data forever. The cybersecurity market offered to fix this issue with backup tools that enabled companies to quickly recover their data. For example, the above-mentioned studio decided to use this method instead of paying ransom and even promised a gift pet to anyone willing to patiently wait.
The introduction of the tools along with local laws banning ransomware payments as terrorism financing contributed to the steady decline of ransomware payments in the past years.
That forced cybercriminals to search for new methods of extortion. Encrypting SaaS data was one of them. The key reason is that restoration in the SaaS environments take more time than in the on-prem solutions as it is limited by the allowed number of API calls.
Longer recovery means longer downtime and hindered business operations. Not all businesses have the privilege to buy waiting with a magical digital creature. Probably that’s the reason why ~41% of victims still decide to pay ransom these days.
A more recent technique to coerce the victims into payment is data theft. Prior to encrypting the victim’s data, criminals would copy it to their local drive. They will then blackmail the victim threatening to make data publicly available online or selling it on the Dark Web to other criminals.
If attackers manage to find the data of third parties (other companies or individuals) in the data they have stolen they can blackmail these third parties. This technique is called triple extortion.
Finally, the new trend is to threaten to report ransomware attacks. Many companies are scared of financial and reputational losses, legal implications or publicity in case authorities or media find out about the attack. The threat to reveal the truth can push them into paying a ransom.
Summing up, extortion is a complex mind game that requires understanding the business operations of a particular target and general human psychology along with the ability to coerce and manipulate others.
Ransomware-as-a-Service (RaaS)
Ransomware attacks have become an increasingly profitable crime. However, to carry out such an attack successfully, the criminal needs to possess a wide variety of skills and even mutually exclusive personal traits.
For example, cybercriminals need to be able to quickly generate new strains of ransomware. It takes time, i.e., long hours of coding. It requires diligence coupled with strong analytical and coding skills.
On the other hand, the most popular delivery method remains social engineering. It requires long hours of research on potential attack targets (both organizations and employees). Furthermore, what comes after a successful attack is a coercion game between the victim and the offender who is trying to extort money. These activities demand high social skills, knowledge of human psychology and the ability to manipulate it.
It was only natural to divide these roles between criminals with respective skill sets and personality traits. Labour division is a development stage in most human societies. It stems from the evolution of technology as it becomes increasingly complex and acquires a longer learning and adaptation curve. Labour division provides higher efficiency while enabling human beings to self-actualize.
Over the past several decades we’ve seen an arms race between cybercriminals and cybersecurity experts. As cyber defenses become more complex, cybercrime requires more refined tools and more intricate attack and extortion methods. That is why we see the labor division in ransomware gangs. RaaS is a product of this division.
Ransomware-as-a-Service is a SaaS application that contains a toolkit necessary for ransomware attacks. It is developed by coders and distributed in the Dark Web. The attackers subscribe to RaaS just as regular people purchase app subscriptions. Then they use it to target potential victims.
This enables RaaS developers to remain in the shadow and leave all the risky work to the attackers. It is also believed that coders sell the RaaS subscription only to the criminals they trust. Sometimes additional tools are purchased by attackers to infiltrate the target’s systems.
Protect your cloud from ransomware. Try SpinOne.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Google Workspace Backup Solutions Comparison
April 26, 2024The number of Google Workspace (formerly GSuite) backup solutions is overwhelming, and choosing the right... Read more
What’s the Best Google Workspace Backup Solution?
April 26, 2024In today’s digital age, businesses rely heavily on cloud-based services like Google Workspace (G Suite)... Read more
Reducing Browser Extension Risk with Spin.AI Risk Assessment + Perc...
April 24, 2024Spin.AI is collaborating with Perception Point: integrating the Spin.AI Browser Extension Risk Assessment within the... Read more